New Years security resolutions for 2006
1. Don’t give personal information to obtain documents on the web
Many sites want you to register to get a free document or certain web page. What do you think they use your information for? Spam, spam and more spam. If you want to get these documents without putting in your personal information, simply put the URL for the site in http://bugmenot.com and get past the registration!
2. Protect against Viruses
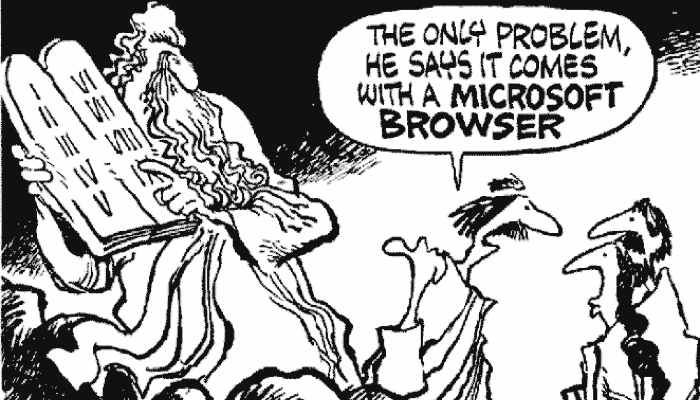
Use Firefox - Many spyware/malware/viruses have code that targets Internet Explorer. Why not use Firefox instead? It’s the web browser that crackers (who make the spyware/malware/viruses) use to browse the web and it stops most pop-up windows, viruses and spyware.
Run AVG - Virus scanners are not equal – look for the one that offers the largest virus database and most frequent updates – today, that virus scanner is AVG, and its free! Just go to http://free.grisoft.com.
Disable Macros - Macro viruses are the easiest viruses to create – after taking a course on Microsoft Office you can make your own…….and you can bet every other 12-year-old who takes Office in grade school has figured that out too. Macro viruses can also spread easily in attachments and can go undetected by virus scanners because virus scanners look for a “footprint” identification and most hackers modify the header of the macro virus to get by this detection (if you change the header, you have a different “footprint”). In the properties/options of your application (e.g. Office, IE, Outlook), you can usually set an option to warn you if a Macro is run or disable macros altogether. Set one of these options!
Use Linux/Mac! According to Sophos (Antivirus software maker), there are 97,467 active Windows viruses. Linux only has 48 active viruses (most of which require you to run a program as the root user to execute). Old Mac OSes (OS 9 or earlier) have 68 known viruses but most of them are more than 10 years old, and the latest Mac OS (OS X) has a whopping 0 known active viruses.
Scan for viruses even if you use Linux/Mac! Although there are essentially no viruses for these OSes, there are still plenty of Antivirus software programs for Linux/Mac, so why? Well, these programs scan for and remove Windows viruses to prevent them from being spread to Windows computers and infecting them.
Viruses also affect VMWare & VirtualPC images. If you run a Windows OS in an emulator such as VMWare or VirtualPC, that OS is as prone to viruses like any regular Windows OS. If you run the “virtual networking” component in these emulators to create a real virtual NIC, this IP is also susceptible to network-based viruses too. I always disable this component – you can still use the network, but it will force the traffic to go through the entire TCP/IP stack on the host OS first.
3. Protect against Spyware/Malware
Spyware currently only exists for Windows computers, but is more serious than most viruses. While viruses typically slow your computer or spread themselves to other files, spyware/malware typically changes registry settings to disable system components (e.g. Display properties) or install software that sends or responds to network traffic. Linux/Mac computers run a type of UNIX, so spyware/malware can’t be run as a privileged user. Windows Vista (the new XP) has a feature like this called User Account Protection (UAP), but it doesn’t work with most spyware/malware. For Windows computers, download and install several different spyware scanners and removers; no single spyware scanner/remover will remove all spyware/malware!
4. Don’t chat without protection
Do you realize that anyone with a packet sniffer can obtain your instant messaging chat conversations? To prevent this, download and use encryption software for your instant messaging. There is encryption software for nearly all types of chat programs. For the MSN, Yahoo, Google, ICQ chat programs, you can use the free SimpLite-MSN program to do this. For iChat, you can use Intego ChatBarrier X3.
5. Protect your home wireless
Who knows how many 10-year kids are using your wireless router at home? Hacking wireless and using Snort/AirSnort is a well-known science – in fact, there are half a dozen books on it at Chapters! And they are good (I admit, I bought a few, and they ARE good).
Ensure that your Wireless Router has WEP or WPA enabled and that the key length is at least 128 bits with a long passphrase. Although WEP is very good, if you are paranoid, WPA is pretty much uncrackable, but every hour you will notice that it pauses your connection for a few seconds while it generates new keys (which is annoying if you use Remote Desktop continuously like I do).
6. Use Protection in Internet Cafés or Public Free Internet Locations
Do you bring your laptop to a public place that offers free Internet? This access is usually unauthenticated and unencrypted, so if you want to use it, you must use it insecurely! To solve this problem, connect to a third-party web service that provides encryption between your laptop and the web service – this web service can then let you browse the Internet freely and no one on the public wireless LAN will see what you are doing. Two examples of these types of services are HotSpotVPN (http://hotspotvpn.com) and T-Mobile Hotspot 802.1x Service (http://www.t-mobile.com).